Denial of service attacks (DoS) have crippled even the likes of Google and Amazon in recent years, topping at a reported 1.1 terabits per second in 2016. But they were a relatively unexplored phenomenon in the year 2000, when three computer scientists from the University of California San Diego set out to find out how prevalent they were.
2017 Test of Time Award from Stanford's Dan
Boneh at USENIX Security in Vancouver on behalf
of Stefan Savage, David Moore and himself.
Their research and resulting academic paper won the Best Paper award when it was presented at the 10th USENIX Security Symposium in 2001. At the time, the study provided the only publicly available data quantifying DoS activity on the Internet. Now, 16 years later, that same paper – “Inferring Internet Denial-of-Service Activity” – has received the 2017 USENIX Security Test of Time Award.
The award was announced today at the opening session of USENIX Security 2017 in Vancouver, Canada. UC San Diego Computer Science and Engineering (CSE) professor Geoffrey M. Voelker accepted the award on behalf of his co-authors, fellow CSE professor Stefan Savage, and their former Ph.D. student David Moore (C.Phil. ’05), who went on to track Internet activity as a project scientist at CAIDA, the Center for Applied Internet Data Analysis. Moore has worked at Google since 2012.
“Test of Time awards are important because they single out research that has a lasting impact despite the rapid change we’ve witnessed in the computing field,” said Dean Tullsen, chair of the CSE department at UC San Diego. “Stefan Savage and Geoff Voelker have done continuously groundbreaking work in cybersecurity for almost two decades, and this award underscores the department’s well-deserved reputation for innovation in areas including security as well as systems and networking.”

technical manager
David Moore (now at
Google)
The Test of Time award recognizes outstanding work in security research that has had a lasting impact on the community. To qualify, a paper must have been presented at a USENIX conference at least 10 years earlier.
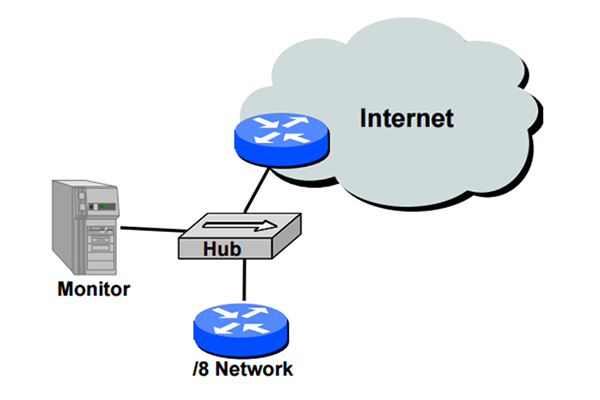
Denial-of-service attacks disable servers linked to the Internet by overloading them with messages, which usually contain false source addresses (“spoofing”) to conceal the location of the attacker. The UC San Diego researchers used key features of those forged signatures to detect and track the attacks. The study found that some attacks flooded their targets with “instantaneous loads” peaking at 600,000 message packets per second – crippling the infrastructure.
“Quantifying the problem was always meant to be the first step toward stopping or at least curbing attacks of this kind,” recalled UC San Diego’s Savage, who co-directs the Center for Networked Systems (CNS) at UC San Diego. “Our 2001 study helped network engineers understand the nature of recent attacks and to study long-term trends and recurring patterns of attacks.”
Award: Stefan Savage (left) and Geoffrey Voelker
In the 2001 paper, the co-authors also developed a novel technique to cut through the clutter of Internet data. Called “backscatter analysis,” the technique involves observing packets from machines that fall victim to DoS attacks by sending responses to the forged IP addresses. By observing these backscatter packets at a statistically significant portion of IP addresses, backscatter analysis can quantify the scope of a DoS attack.
For their study, Moore, Voelker and Savage looked at three week-long datasets in February 2001 to assess the number, duration and focus of attacks, and to characterize their behavior. In the space of one week, they observed more than 12,000 attacks against more than 5,000 distinct targets, ranging from well-known e-commerce companies such as Amazon, to small foreign Internet Service Providers (ISPs) and – remember, this is 16 years ago – dial-up connections. “At the time,” said Voelker, “our work was the only publically available data quantifying denial-of-service activity in the Internet.”
The technique produced an estimate of worldwide malicious DoS activity – with approximately 4,000 sites experiencing DoS attacks weekly (as of 2000), and over 12,000 attacks over three weeks.
2001 paper honored at USENIX Security
The 2001 study also was among the first to use the quantitative data to characterize the victims of DoS attacks, which seem almost quaint in retrospect. “Only five percent of attacks targeted infrastructure such as routers and name servers,” explained Voelker. “There were a few very large attacks against broadband, and up to 20 percent of attacks were targeted at home machines – evidence that minor DoS attacks were used for personal vendettas.”
The CSE department at UC San Diego is no stranger to winning Test of Time awards handed out by USENIX at a few of its major conferences. Already in 2017, CSE professor George Porter shared in the Test of Time award at the USENIX Symposium on Networked Systems Design and Implementation (NSDI) for “X-Trace: A Pervasive Network Tracing Framework”, originally published at NSDI 2007. And in 2016, former CSE professor Amin Vahdat and his co-authors received the NSDI Test of Time award for a paper presented at NSDI 2006.
The 26th USENIX Security Symposium takes place Aug. 16 to 18 in Vancouver, Canada. UC San Diego’s CSE department is well represented on the conference program. Ph.D. students including Craig Disselkoen, David Kohlbrenner, Zhaomo Yang, and Brian Johannesmeyer have papers on the program, together with faculty including Leo Porter, Dean Tullsen, Hovav Shacham, Sorin Lerner and research scientist Kirill Levchenko. Their three papers include:
- Prime+Abort: A Timer-Free High-Precision L3 Cache Attack Using Intel TSX, by Craig Disselkoen, David Kohlbrenner, Leo Porter, and Dean Tullsen
- On the Effectiveness of Mitigations against Floating-Point Timing Channels, by David Kohlbrenner and Hovav Shacham
- Dead Store Elimination (Still) Considered Harmful, by Zhaomo Yang, Brian Johannesmeyer, Sorin Lerner and Kirill Levchenko (and Aalborg University’s Anders Trier Olesen)
CSE professor Deian Stefan will chair a session on “Side-Channel Countermeasures” on the first day of the conference.
Related Links
2001 Paper: Inferring Internet Denial-of-Service Activity
USENIX Security Symposium 2017

